CheckRed – How CSPM Solutions Help MSPs and MSSPs Ensure Cloud Security Compliance
With the rapid advancement of technology, organizations are adopting IT solutions to stay productive and run their operations efficiently to stay in the competitive environment. With this continuous development of technology, cloud computing has become an essential component of companies’ IT infrastructure.
However, the reliability of technological infrastructure comes with cyber threats. That’s when MSP and MSSP come into play. They provide top-notch services to companies to protect their data from malware, phishing, or ransomware attacks.
It is essential for managed service providers (MSPs) and managed security service providers (MSSPs) to prioritize cloud security by adopting Cloud Security Posture Management (CSPM) solutions. This technology is designed to detect and prevent data misconfiguration and threats that can lead to breaches of data and compliance violations.
If you are looking for CSPM solutions, you can go with CheckRed. To know further, read through this article and understand how CSPM solutions help MSPs and MSSPs for cloud security compliance. Also, learn about the Future of Cloud Computing in this guide.
What is Cloud Security Posture Management?
Cloud Security Posture Management(CSPM) is a component of IT tools devised to identify misconfiguration problems and compliance risks in the cloud infrastructure.
It contains Infrastructure as a service (IaaS), Software as a service (SaaS), and platform as a service (PaaS). CSPM solutions enable constant monitoring of cloud infrastructure for any gap in security policy enforcement.
CheckRed’s Contribution to CSPM
With CheckRed, an organization can meet its compliance needs and security posture with ease. It gives businesses access to a centralized platform that allows SaaS and cloud security posture monitoring and visibility collectively.
Its alert system immediately identifies any possible threat that leads to rapid action and prompt response. One of its key advantages is that it provides customized services that meet the particular demands of each organization.
With the help of customization, integration of the tool into the existing system becomes a seamless process that enables the smooth functioning of daily operations. CheckRed is a helpful tool for every MSP and MSSP who is looking for supervision of security posture and compliance requirements of their clients.
Importance of CSPM

The protection of data is important in any cloud service, and CSPM can play a key role in protecting against any cyber threat significantly.
With the increasing number of organizations using these services, the risk associated with data security is also surging rapidly.
According to Gartner, the reason behind data breach is cloud misconfiguration. By utilizing CSPM, you can protect your company against the following issues:
- Issues related to legal and regulatory compliance
- Misconfiguration
- Illegal access to your data
- Hijacking of account
- Lack of visibility
- Insecure interfaces
- Data sharing with external sources
- Regulation issues
- Challenges associated with cloud governance
As per Verizon’s 2023 Data Breachment Investigation report, misconfigurations are among the top three leading causes of breach of data, accounting for 20% of them in 2023.
How Does Cloud Security Poster Management Work
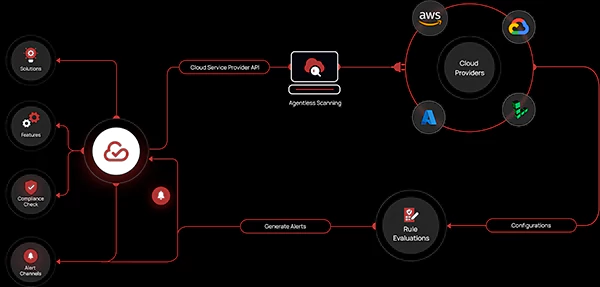
CSPM tools are mapped out in a way to identify and improve the cloud misconfiguration issues. Its basic functionality is to constantly monitor and scrutinize cloud assets across multiple cloud providers.
Whenever the new cloud service is employed or if there is a configuration change, the tool detects and automatically updates to make sure that it complies with security requirements.
CSPM solutions are not similar to most of the securities that require agents or appliances. It offers API-driven solutions that get connected with your cloud environment for security and compliance.
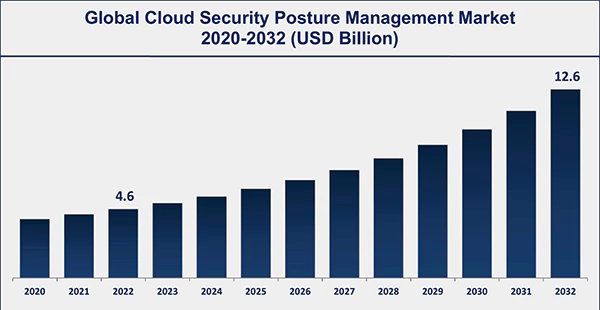
The below graph represents the continuously increasing global market size of Cloud Security Posture Management.
Benefits of Cloud Security Posture Management
CSPM has multiple benefits to offer for threats, abuses, configuration errors, and compliance issues. Below are some advantages of it-
CSPM Provides Visibility
It is essential to attain visibility into all the cloud services spread across cloud providers. CSPM solutions provide visibility across multi-cloud and cloud environments by analysis and normalization of data resources along with creating an inventory of cloud assets.
Detection of Risks Proactively
One of the best advantages of CSPM is that it can detect the risk before the attacker can exploit the data by automatic identification of security gaps, misconfiguration, and vulnerabilities.
Do you know?
85% of organizations will be cloud-first by 2025.
Smooth Integration of CSPM into the System
Launch and configuration of CSPM can be done easily across large environments with AI and automation to recognize threats quickly, expand and increase threat investigation, and help in automatic remediation. It ensures a link to the existing system of management to mitigate the risk through a smooth process.
Helps with Recommendations
You can get insights about the state of the system and suggestions for security posture.
As updates regarding regulatory compliance occur regularly, you can employ CSPM to get the updates and automatic implementation of these updates to enhance the security posture and misconfiguration.
CSPM examines the cloud environment thoroughly to identify risks and provide protection against threats.
Conclusion
Cloud Security Poster Management is crucial for organizations to protect against any threats. Businesses, by utilizing CSPM, discover threats, misconfiguration, and compliance violations in public cloud environments.
CSPM provides numerous benefits and organizations get overwhelmed while selecting adequate tools to get the right solution. By choosing CheckRed, organizations can get maximum results with an effective approach.
